Overview
This article shows you how to test your Jive LDAP integration settings.
This process is useful in both setting it up for the first time and when the LDAP sync is not working, helping to rule out issues on the LDAP side.
It may help to troubleshoot the error "Error connecting to the directory server" and "Ensure that the directory server is running at the specified host name and port and that a firewall is not blocking access to the server".
Diagnosis
If your LDAP is already setup, but it is not working at the moment, it is worth checking the status of the LDAP connection from inside your instance.
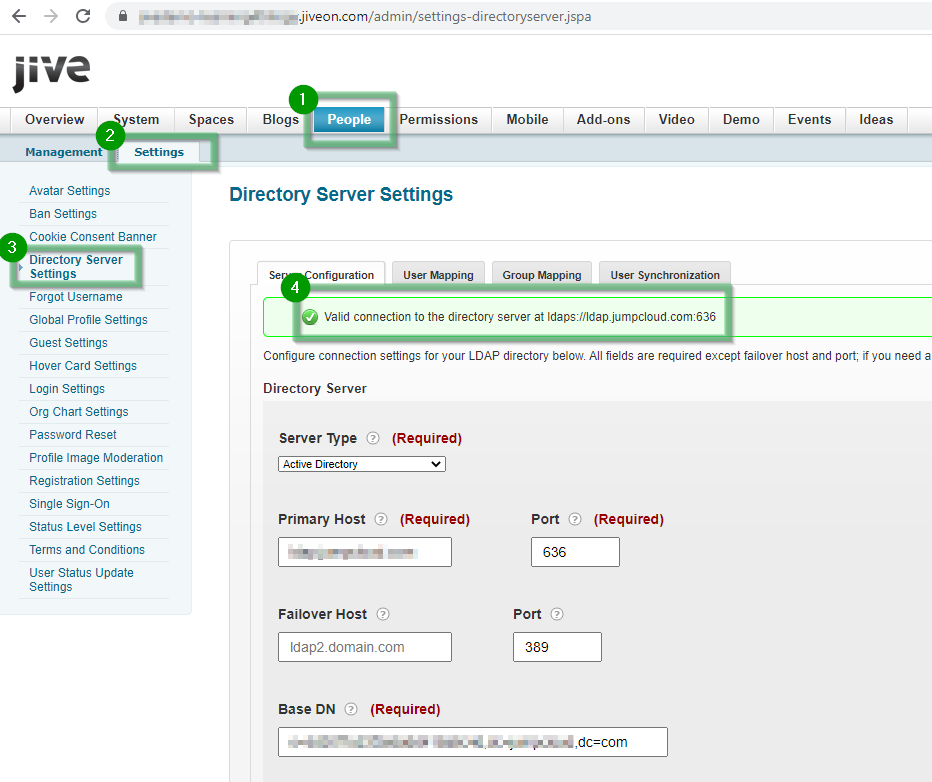
Go to Admin Console > People > Settings > Directory Server Settings:
Check the error message (if any) that is appearing in the upper part, or, as in this case, a message saying that a valid connection was established. Ensure the name of your LDAP server is correct.
Scroll down to the bottom of the page, enable Debug, and use the button "Test settings":
If this is a production instance, remember to disable the "Enable Debug", after the testing.
If the connection fails, you may get the error:
"Error connecting to the directory server at <serveraddress>. Ensure that the directory server is running at the specified host name and port and that a firewall is not blocking access to the server."
Solution
The procedure described here will allow you to test your LDAP connection outside of Jive, from your client machine.
-
Get the right tool for the job.
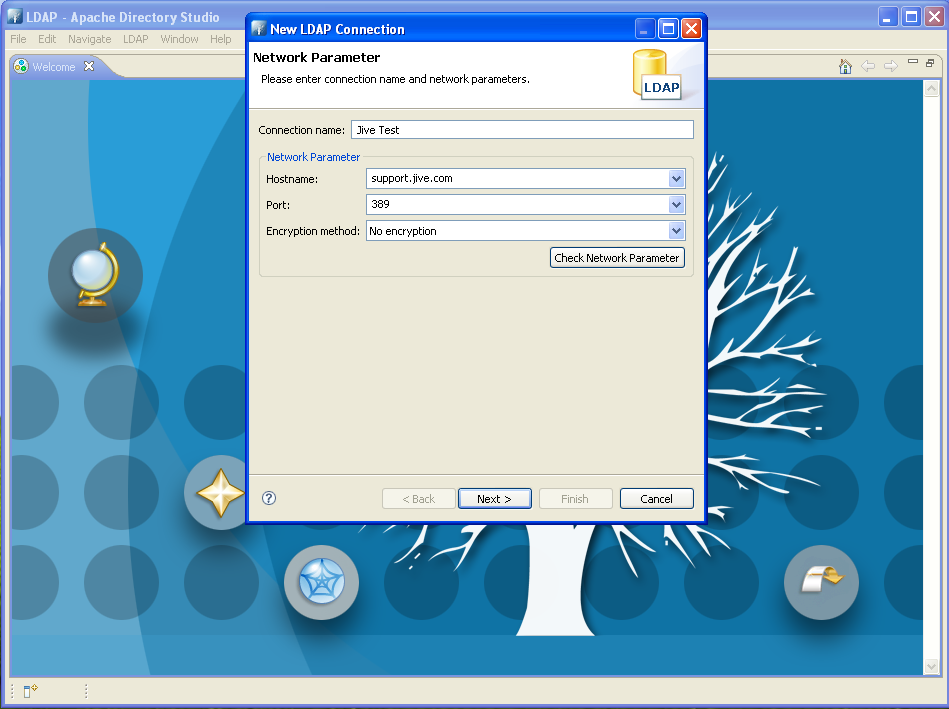
It is recommended to use Apache Directory Studio for its ease of use and rich set of functionality. It's free to download and installs in minutes. As a prerequisite, you will also need the Java Runtime Environment (JRE) installed. -
Establish a connection.
Once you have Directory Studio installed, start it up, then go to LDAP > New Connection:
- The Hostname and Port here map to the values you'll use when establishing your Jive LDAP connection. They map to the system properties
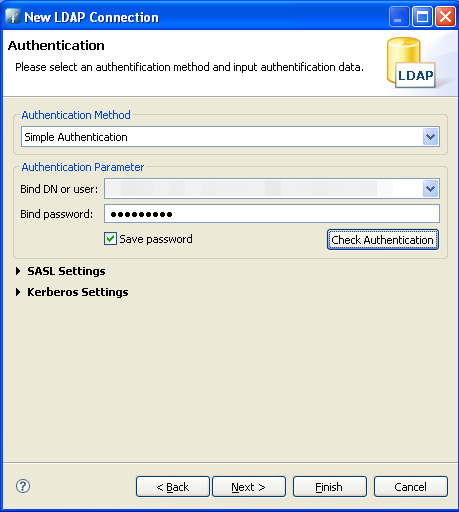
ldap.hostandldap.portin Jive. - The next screen asks for the credentials for the service account you'll use to bind and query LDAP:
- Use the DN of the user that you will use for the
ldap.adminDNproperty. - Once you have authenticated, go to the next screen and ensure that Follow Referrals automatically and the Paged Search controls are selected. These mimic the default settings of Jive's LDAP integration. If any adjustments to these settings are necessary, it can be detected during this testing phase.
- Click Finish to complete the new connection setup process.
- The Hostname and Port here map to the values you'll use when establishing your Jive LDAP connection. They map to the system properties
-
Test your LDAP searches.
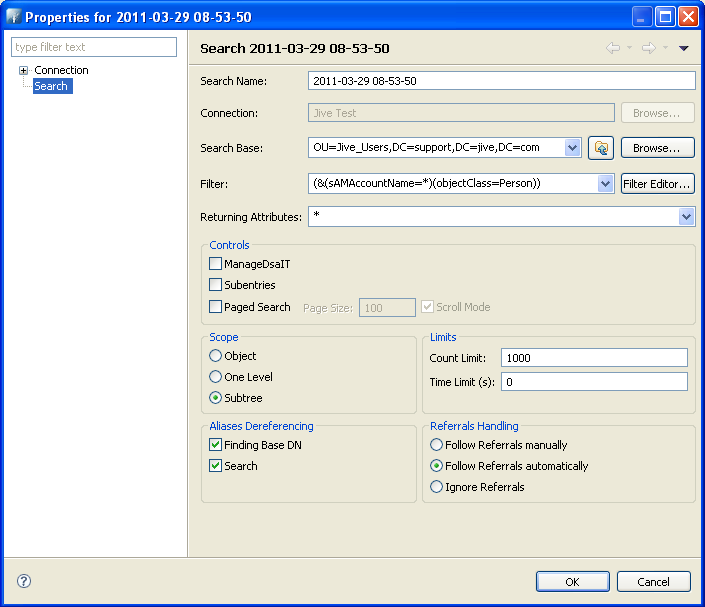
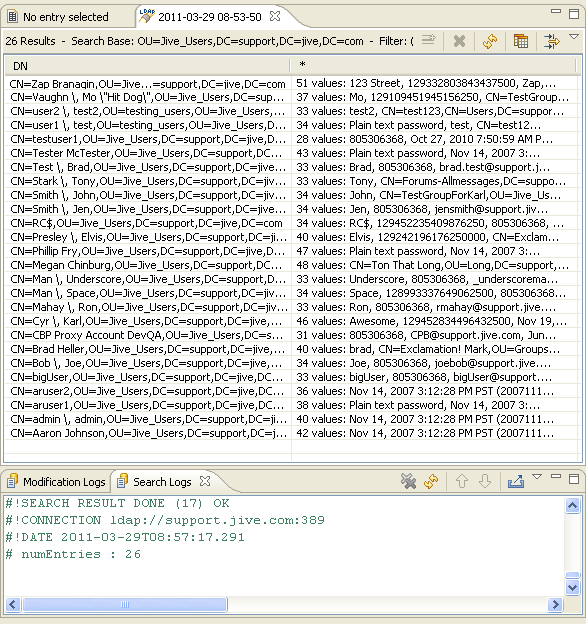
- Click on the flashlight icon and select LDAP Search. Be sure to select your newly created connection, then enter search criteria to test your user and group search filters:
- For the Search Base, use the base DN you intend to use to connect to Jive (
ldap.baseDN). Specify a search filter (ldap.searchFilter) you will use to retrieve users. Set Returning Attributes to * to retrieve all information for all user records. Click OK and check your results.
- If you receive unexpected results, try adjusting the filters to match your needs. Active Directory, in particular, tends to have a large number of non-human principals return in LDAP results, so filtering on a clause such as objectClass=Person is recommended. You can also use this search functionality to test your group search filter
ldap.groupSearchFilter.
- Click on the flashlight icon and select LDAP Search. Be sure to select your newly created connection, then enter search criteria to test your user and group search filters:
Just make sure that both the client from which you are performing this test and the Jive instances are not blocked by any firewall on your corporate Active Directory / LDAP server.
If you get the same errors from your machine, most likely it is an issue related to your LDAP server. If, instead, the queries from your machine work without issues, most likely it is a problem on the Jive side, and it is better to open a ticket to Support, making sure to detail the troubleshooting steps performed.
Additional information and caveats:
- You may notice that Jive specifies the default search filter for Active directory as
sAMAccountName={0}, but the {0} notation will not retrieve any results in Directory Studio. This is because the {0} is a notation Jive uses for its own purposes, while * is the standard LDAP wildcard character. It is recommended to keep thesAMAccountName={0}notation in the Jive search filter even though you will need to change it to return results in your testing. - Here are a few sample filters you may want to experiment with when testing your configuration:
- Find all groups:
(objectClass=Group) - Filter out all users who are disabled in Active Directory:
(&(sAMAccountName={0})(!(userAccountControl:1.2.840.113556.1.4.803:=2))) - Find all users who belong to a particular group:
(&(sAMAccountName=*)(objectClass=Person)(memberOf=CN=FilterGroup,OU=Jive_Users,DC=support,DC=jive,DC=com)) - Find all users in the TestABC department:
(&(sAMAccountName=*)(department=TestABC))
- Find all groups:

Priyanka Bhotika
Comments